Introduction
The NAVSTAR GPS has been established and has been operated up to now by the US department of defense (DOD). Consequently, GPS was designed to provide position, navigation and time (PNT) to the US military and its allies. However, today’s reality is that GPS is used for a multitude of applications mostly by civil users and applications, outnumbering their military counterparts by far. The European brother of GPS, Galileo, was designed as a civil system, but also for Galileo both civil and military use is certain. Similar statements can be made for other Global Navigation Satellite Systems (GNSS), which are emerging or are already fully operational, like the Russian GLONASS and the Chinese BeiDou. Besides the provision of navigation information for aeronautical, maritime, and ground based users, the civil use of GNSS has become a backbone of our infrastructure. Most Critical Infrastructure and Key Resources (CIKR) sectors are relying on GNSS: In the communications and IT sector, GNSS timing information is used for network synchronization as well as frequency generation and stabilization. In the energy sector, the phase synchronization within the power grid is based on GNSS, and so is the process scheduling and control of many applications within the oil, gas, and chemical industry sectors. Last but not least, the worldwide accurate time stamping of data within the banking & finance sector is nowadays unthinkable without GNSS.
The greater the dependency on GNSS, the more important is the availability and reliability of GNSS PNT information. The main threats jeopardizing GNSS availability and reliability are jamming and spoofing.
Jamming is a synonym for intentional interference, which is the deliberate radiation of electromagnetic signals at GNSS frequencies. Hereby, the aim is to overpower the extremely weak GNSS signals so that they cannot be acquired and tracked anymore by the GNSS receiver. Besides military jammers, which are an integral part of navigation warfare (NAVWAR) strategies, so-called Personal Protection Devices (PPD) are encountered more and more frequently. PPDs are small, light-weight jammers that are easily available via the internet. Their use is of course forbidden in the majority of countries; however, the possession of these devices is not regulated everywhere with the same strictness. Besides intentional interference, unintentional interference also occurs. Some GNSS bands are shared with certain radars, as well as amateur radio. Other sources are Distance Measuring Equipment (DME) used for airplane navigation, TV harmonics, as well as malfunctioning electronic equipment.
Spoofing, on the other hand, is the generation and transmission of fake GNSS signals, with the aim to lead a GNSS receiver astray, possibly without the GNSS receiver being aware of the attack. Of course, spoofing is technically more challenging than jamming, as the complex GNSS signal structures have to be reproduced, usually for several GNSS signals in parallel. Meaconing, the little brother of spoofing, is the re-transmission of received GNSS signals. This avoids the burden of implementing the generation of the complex GNSS signal structures and also causes the GNSS receiver to provide erroneous PNT information, because the reception and re-broadcast process changes the relative delays of the GNSS signals as seen by the receiver, compared to the relative delays of the authentic GNSS signals at the receiver’s location.
In the following sections, today’s reality of jamming and spoofing is outlined, and possible countermeasures are discussed. Special attention is paid to server-assisted techniques, which have the potential of enabling the easy use of encrypted GNSS services for authorized users. Finally, conclusions are drawn.
Jamming: Events and countermeasures
Over the last years, several reports on the use of military jammers, or jammers operated by governmental organizations, have surfaced. This includes reports on the use of Russian GPS jammers during the Iraq wars, reports on North Korea jamming towards South Korea, or an incident where the US Navy accidentally knocked out GPS for three days in the San Diego harbor in January 2007 by means of a jammer. However, for obvious reasons, not too much information can be found on the details of these incidents.
The largest number of jamming events is caused by PPDs. A famous example is the case of a truck driver regularly passing by Newark airport with his PPD in operation, causing significant problems for the receivers of the ground based augmentation system (GBAS) installed nearby. To the knowledge of the authors, this is also the first case where a considerable fine was imposed on the responsible person for causing the jamming [1]. However, according to [2], several ten thousands of jamming events have been registered in the last few years. The fact that these jammers can be purchased easily via the internet surely contributes to the high number of jamming events, see Figure 1. According to the law in most countries, the purchase of the device itself is legal, but not its operation.
Most PPDs emit continuous wave (CW) or chirp signals, the latter can be seen as a CW which constantly changes its center frequency to cover a large bandwidth. While a single CW can be countered – at least in theory – relatively easily by means of a notch filter tuned to the CW frequency, the mitigation of chirps is more complex. This is one motivation of the jammers for producing chirp signals; another motivation is that often low quality electronics are used which do not allow for generating a CW with sufficient precision to hit the targeted GNSS frequency.
A vital means to counter jammers is the use of an array antenna, which either is able to steer the radiation pattern of the array to form a spatial null towards the jammer, or to provide additional gain towards the satellites. However, such controlled radiation pattern antennas (CRPA) are military technology and the availability for civil users is an exception. As stated previously, a notch filter can be used in the receiver front-end to mitigate CW signals, and to a certain extent, adaptive notch filters can be used to counter chirp signals as well, provided that the chirp rate is not too high. Interestingly, low-cost mass market receivers are often more robust against chirp jammers than professional receivers. The reason for this is that mass market receivers often have very narrow front-end filters, so that during a good portion of a chirp sweep cycle, the chirp is suppressed by these filters. Professional receivers have a wider front-end bandwidth, which allows for more accurate measurements but also increases their vulnerability to chirp jammers. Wideband GNSS signals like Galileo E5 or Galileo PRS allow for the development of advanced mitigation techniques, which allow closing this gap. However, it has to be understood that the vast majority of GNSS receivers sold today do not implement any countermeasures against jamming.
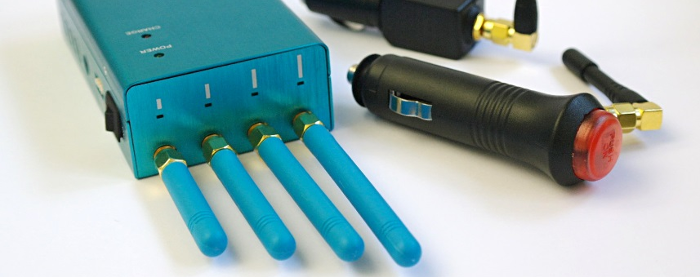
Figure 1: Generic PPDs bought by Fraunhofer IIS over the internet without any issues (used under controlled conditions for research purposes only)
Spoofing: Events and countermeasures
The implementation of a spoofing attack is considerably more complex than the implementation of a jamming attack, especially if the attack is supposed to remain undetected. In order to avoid discontinuities when a tracking loop transfers lock from the original satellite signal to the deceptive signal, the generation of the deceptive signal has to be synchronized with the satellite signal at the location of the antenna of the receiver under attack. In case the spoofer cannot be installed onboard the vehicle carrying the receiver under attack, the receiver position has to be determined and tracked by some means. Given the greater technical complexity and the fact that the motivation for implementing a spoofing attack is less obvious than the motivation for using PPDs, it is not surprising that the number of reports on spoofing incidents is smaller than for jamming incidents. Nevertheless, some events are known, however not all of them are confirmed. On December 4th, 2011, Iran captured a U.S. Lockheed Martin RQ-170 drone, claiming to have spoofed GPS. Other reasons, e.g. GPS jamming or jamming of the communication link are also feasible, possibly triggering an emergency landing procedure. Some reports connect the collision of USS John S. McCain with another vessel on August 21, 2017, with spoofing. An explanation for this suspicion is not given. The technical feasibility of spoofing attacks was demonstrated by the team of Todd Humphreys at the University of Austin, Texas, in 2012. With custom-built spoofing equipment, the spoofing of a drone, an $80M yacht, and the time of a power grid was demonstrated. The interest in spoofing was recently boosted by the advent of “Pokémon Go”, a smartphone augmented reality game which connects the GPS user location to the occurrence of items that have to be collected. The motivation for spoofing in this context is to trick the smartphone into believing the player would be at certain locations, while the player would actually not leave their couch. Since 2016, the software for building a “Pokémon Go” spoofer based on HackRF hardware is freely available, the total cost amounting to below 250€. An unintentional spoofing incident happened on November 28, 2017, at the ION GNSS+ conference in Portland, Oregon, one of the largest navigation conferences worldwide. There, a manufacturer of a Radio Frequency Constellation Simulator (RFCS) accidentally emitted spoofing signals within the exhibition hall. RFCS allow for specifying a scenario essentially consisting of a receiver trajectory and reception conditions, and then generate an RF signal that is similar to the signal provided by a GNSS antenna when operated in such a scenario in the real world. RFCS are used for receiver testing and characterization. The accidental emission of the RFCS signal within the exhibition hall caused several smartphones to transfer lock to the spoofing signal, and because the time of the RFCS scenario was set to the future, several Apple iPhones lost their security certificates and could not be unlocked anymore.
The impact of the latter unintentional and consequently not very sophisticated spoofing showed that no countermeasures were in place. Viable countermeasures against spoofing are array antennas. However, against simple spoofing attacks, the monitoring of certain GNSS receiver Key Performance Indicators (KPI) can be successful, such as monitoring for clock jumps, not plausible signal-to-noise density ratios, or differences between code and carrier measurements. Furthermore, cryptographic techniques can be effective: One example is the Galileo Public Regulated Service (PRS), similar to the GPS military P(Y) and M-Code, which uses spreading codes that are generated by cryptographic means, and also uses navigation message encryption. Without appropriate keys and crypto algorithms, a spoofer is unable to produce such signals. Soon, the Galileo E1 Open Service will offer Navigation Message Authentication (OS-NMA), which leads also to a signal consisting of some parts that cannot be generated by a spoofer. Similar encrypted spreading code techniques are also planned for the Galileo Commercial Service (CS).
As described in the introduction, meaconing is a technique closely related to spoofing, but avoiding the need to be able to actively produce the GNSS signal structure. Several meaconing events have been reported and confirmed: In 2012, a GPS repeater used in a hangar at Hannover airport, Germany, caused pull-up alarms in starting and landing aircrafts, triggered by the GPS receivers onboard these planes which had transferred lock to the repeater signal. The repeater was intended to provide GNSS reception to the GNSS receivers onboard the planes inside the hangar, but unfortunately the hangar doors had been left open temporarily. In [3], incidents in the Black Sea occurring in June 2017 are reported, where the GPS receivers on board of more than 20 ships showed positions jumping between the true position and another position, in this case the position of Gelendzhik airport more than 30 kilometers away. [4] reported a similar behavior of GPS receivers in the vicinity of Moscow’s Red Square, which showed positions of the Wnukowo airport. Such observations indicate meaconing attacks. A motivation for such an attack can be to trigger the geo-fencing mechanisms implemented in drones, in order to prevent drone operations in certain areas. The geo-fencing mechanisms implement no-fly zones over airports, so that if such a no-fly zone is reached, an automatic descent is initiated.
Against meaconing, i.e. the use of repeaters, similar countermeasures apply as against spoofing. The only exception is that cryptographic techniques, i.e. encrypted navigation messages, spreading code generation by cryptographic means, and navigation message authentication, do not always help against meaconing, depending on the receiver’s architecture and anti-replay features. The reason is that unlike for spoofing attacks, the repeater does not need to know the structure of the GNSS signal it re-transmits.
The future of reliable, user-friendly PNT: Server-assisted positioning
As discussed above, the use of encrypted GNSS services like Galileo PRS, Galileo CS, GPS P(Y) and M-code is an efficient protection against jamming and spoofing. These services are – for good reasons – only accessible to authorized users. In case of GPS, the authorized users are the military. For Galileo PRS, each PRS member state decides on its own about its authorized users in line with the Decision 1104 on the rules for access to PRS. For Galileo CS authentication, the access policy is not defined yet. However, even for an authorized user, the access to an encrypted GNSS service does not come by itself: With a conventional encrypted GNSS services receiver, the user needs appropriate keys as well as a key distribution system capable of administering a large number of users. Furthermore, the receiver needs to implement various classified algorithms, key storage and administration, as well as measures for tamper protection in a so called security module (SM). Furthermore, this receiver with SM needs to be certified in order to obtain an unclassified-when-keyed status – otherwise, the receiver could only be operated in classified areas. Even an unclassified-when-keyed receiver represents a controlled item, which means that it has to be registered throughout its lifetime. Basically, the handling of a controlled item is comparable to the handling of a firearm, which is a huge obstacle for many potential user groups of such encrypted GNSS services, e.g. fire fighters or federal agencies for disaster relief. Server-assisted techniques can offer a solution to this problem. With server-assisted techniques, the SM is outsourced to a secure server environment, where all the security related processing as well as key handling is carried out. The user receiver itself stays as simple as possible with only minimal security handling, if any. Today, three major groups of server-assisted positioning techniques are known:
- Sampling & Processing (S&P). In S&P, the user receiver is a simple bit grabber of the raw data signals from the sky. It acquires a short snapshot of baseband samples and sends it to the assistance server via a communication link or other means of transmission. The assistance server contains an appropriately keyed SM, and is able to calculate a PNT from this snapshot. The PNT may or may not be sent back to the user terminal, depending on the application. The access to the encrypted GNSS service is controlled via the communication link, the user receiver has to authenticate itself upon establishment of the connection, and the assistance server decides whether access to encrypted and reliable PNT is granted. The main advantage of this approach is its simplicity; the main drawback is that the required communication bandwidth rises with the number of user receivers.
- Spreading Code Transmission (SCT). In SCT, the assistance server provides short spreading code sequences to the user terminals, shortly after the corresponding GNSS signals have been sent. The user terminal expects this provision of spreading codes, and records a sample snapshot for a matching time interval. When the spreading code sequences are subsequently obtained from the assistance server, the user terminal can generate appropriate encrypted signal replicas and correlate with the signal-in-space (SIS) sample snapshot to obtain relative pseudoranges. With ephemeris data provided by the assistance server as well, the user terminal is able to calculate a PNT. Access control to the encrypted GNSS service is also established via the communication link, the assistance server decides whether or not a user terminal is provided with short spreading code sequences and ephemeris data. The advantage of this technique is that the required communication bandwidth does not necessarily rise with the number of user receivers allocated to the assistance server.
- Pre-calculate & Process (P&P). P&P is the newest technique, and is tailored to applications where the mission duration is limited to a few hours. The principle of operation is the same as with SCT; the difference is that the short spreading code sequences that are provided in SCT during the mission are in P&P pre-calculated and stored before the mission in the user receiver. Access control to the encrypted GNSS service is established by the fact that after the mission duration of a few hours, no more spreading code sequences are available in the user receiver, and the user receiver is automatically excluded from the encrypted service. This is a distinct advantage for applications where the loss of the user receiver is a risk.
These server-assisted techniques are very promising compared to the conventional use of encrypted GNSS receivers, as user receivers with a low size, weight and power (SWaP) footprint can be built with components off the shelf (COTS), keying issues can be circumvented, and an easier handling can be expected. The huge potential of these techniques has been recognized very early by the ESNC, where proposals for server-assisted PRS techniques where selected as the Bavarian winners in 2012 (S&P) [5], overall winners in 2014 (SCT) [6] and 2017 (P&P) [7], including the ESNC special prize on Galileo PRS. However, the major problem with these techniques manifests in the fact that the regulatory framework that clearly defines the use of these techniques and the constraints that apply is not yet available or clearly defined.
Conclusion
The backbone of our infrastructure is relying on GNSS. The implementation of countermeasures against jamming and spoofing threats considerably drags behind the speed with which the use of and dependence on GNSS increases. Jamming is already recognized as a serious problem and the awareness w.r.t. spoofing at least slowly increases. In order to achieve an adequate level of GNSS resilience considering the importance of GNSS, the efforts in this direction have to be increased. Encrypted GNSS services provide unique capabilities to enhance the security of GNSS; server-assisted techniques could play a key role as an enabler for the widespread and user-friendly use of these encrypted GNSS services. In order to establish the required regulatory framework, a common effort e.g. on European level is required.
References
[1] InsideGNSS, “FCC Fines Operator of GPS Jammer That Affected Newark Airport GBAS “, August 31, 2013, http://insidegnss.com/fcc-fines-operator-of-gps-jammer-that-affected-newark-airport-gbas/
[2] Heise Online Newsticker, “GPS unter Beschuss: Jamming und Spoofing nehmen bei Ortungssystemen zu”, 2nd of May, 2018, https://www.heise.de/newsticker/meldung/GPS-unter-Beschuss-Jamming-und-Spoofing-nehmen-zu-4038137.html
[3] Jones, M., “Spoofing in the Black Sea: What really happened.”, GPS World, October 11, 2017, http://gpsworld.com/spoofing-in-the-black-sea-what-really-happened/
[4] Süddeutsche Zeitung, “Rund um den Kreml spielt das GPS verrückt”, 31st of October 2016, https://www.sueddeutsche.de/digital/moskau-lost-in-navigation-1.3228389
[5] Rügamer, A., Stahl, M., “Privacy-Protected Localisation and Authentication of Georeferenced Measurements with Galileo PRS”, ESNC 2012, https://www.esnc.eu/winner/privacy-protected-localisation-authentication-georeferenced-measurements-galileo-prs/
[6] Kogler, W., Wendel, J., “Low-Cost PRS Receiver for Positioning and Timing Enabled by an Assistance Server”, ESNC 2014, https://www.esnc.eu/winner/low-cost-prs-receiver-positioning-timing-enabled-assistance-server/
[7] Rügamer, A., Wendel, J., “SORUS – Spoofing-Resistant UAVs”, ESNC 2017, https://www.esnc.eu/winner/sorus-spoofing-resistant-uavs/
About Jan Wendel
 Jan Wendel received the Dipl.-Ing. and Dr.-Ing. degrees in Electrical Engineering from the University of Karlsruhe in 1998 and 2003, respectively. From 2003 until 2006 he was an assistant professor at this University. From 2006 to 2009, Jan Wendel was with MBDA in Munich. In 2009, he joined to Airbus Defence and Space GmbH in Munich, where he is involved in various activities related to satellite navigation.
Jan Wendel received the Dipl.-Ing. and Dr.-Ing. degrees in Electrical Engineering from the University of Karlsruhe in 1998 and 2003, respectively. From 2003 until 2006 he was an assistant professor at this University. From 2006 to 2009, Jan Wendel was with MBDA in Munich. In 2009, he joined to Airbus Defence and Space GmbH in Munich, where he is involved in various activities related to satellite navigation.
About Alexander Rügamer
 Alexander Rügamer received his Dipl.-Ing. (FH) degree in Electrical Engineering from the University of Applied Sciences Wuerzburg-Schweinfurt, Germany, in 2007. Since then he has been working at the Fraunhofer Institute for Integrated Circuits IIS in the Field of GNSS receiver development. Since April 2013, he is head of a research group dealing with secure GNSS receivers.
Alexander Rügamer received his Dipl.-Ing. (FH) degree in Electrical Engineering from the University of Applied Sciences Wuerzburg-Schweinfurt, Germany, in 2007. Since then he has been working at the Fraunhofer Institute for Integrated Circuits IIS in the Field of GNSS receiver development. Since April 2013, he is head of a research group dealing with secure GNSS receivers.